Maybe you already know about Cilium, You don’t?
Go read https://docs.cilium.io/en/stable/overview/intro/ and come back !!
Hello again!
So now you want to learn about Cilium BGP functionality, for me this is one of the most exciting features of Cilium, maybe the reason is the addiction that I already have for BGP, who knows (AS207036). Back to the point, with Cilium you can establish a BGP session with your routers (Tor, border, or core, you decide.) and announce PodCIDR or LoadBalance for services.
For this learning exercise, we will use Kind and other tools to run a K8s cluster locally on any Linux (Windows or MacOS) machine. There is a lot of info on the internet on how to get Kind up and running and even how to install Cilium, I decided to build a collection of Cilium Labs (ciliumlabs) to speed up the process of getting a Cilium testing environment up and running.
First, go and clone the repo, all the information is on the README of each lab type, in this case, bgp/README.md is the one with the steps to get this ready, but we first need to install the prereqs. The prerequisites are listed in the main README file. In my environment, all this is met so I can proceed with the lab creation.
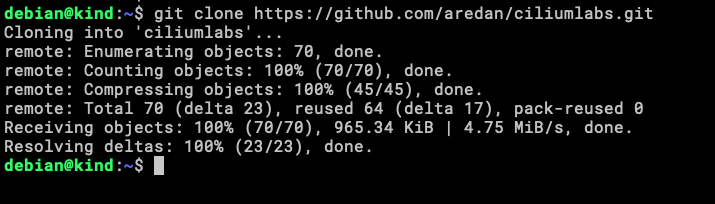
Clone the repo to your local machine.
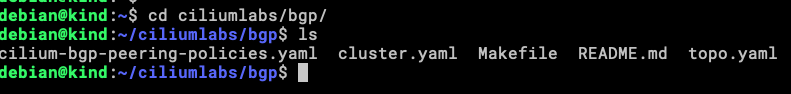
We are doing the BGP Lab, these are the files in that specific directory.
cilium-bgp-peering-policies.yaml – YAML file with the configuration needed to start the BGP session with Tor0 and Tor1 from the k8s workers.
cluster.yaml – configuration file for Kind cluster.
topo.yaml – configuration file for containerlab.
There is a Makefile, an easy way to run tasks, you can read this file to understand the workflow to start the Lab, the fastest way is just to run make.
Let’s see what we have here.
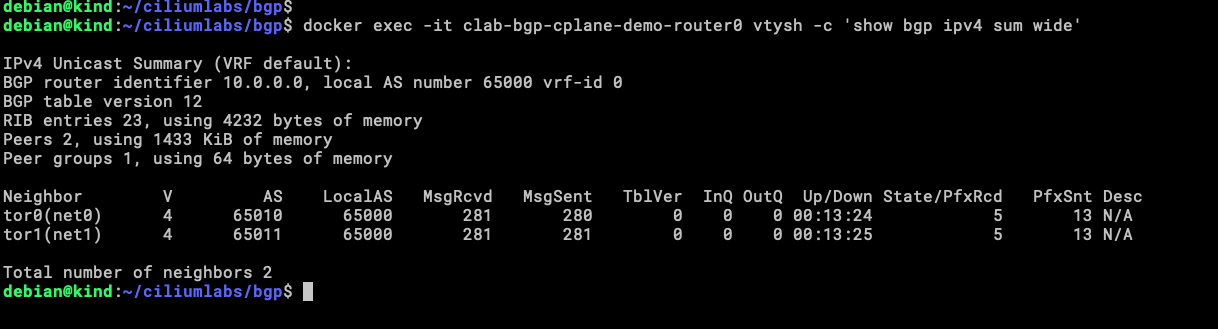
Looking at router0, we can see that both tor0 and tor1 established the BGP peering and router0 is receiving prefixes from those tor routers.
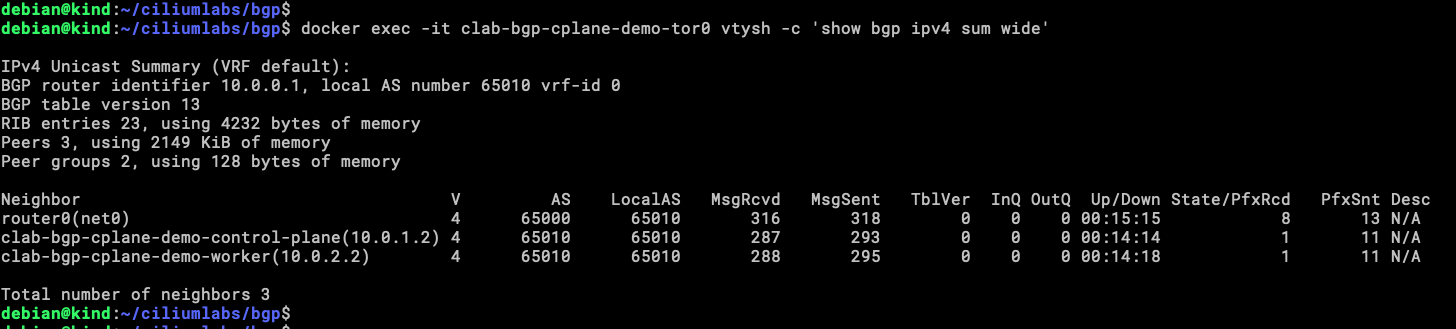
In this Lab topology tor0 is part of the Rack0 segmentation, in this rack is the participation of the control-plane node and a worker (you can see this in the yaml files for kind and containerlab). They are establishing BGP peering and exporting routes!
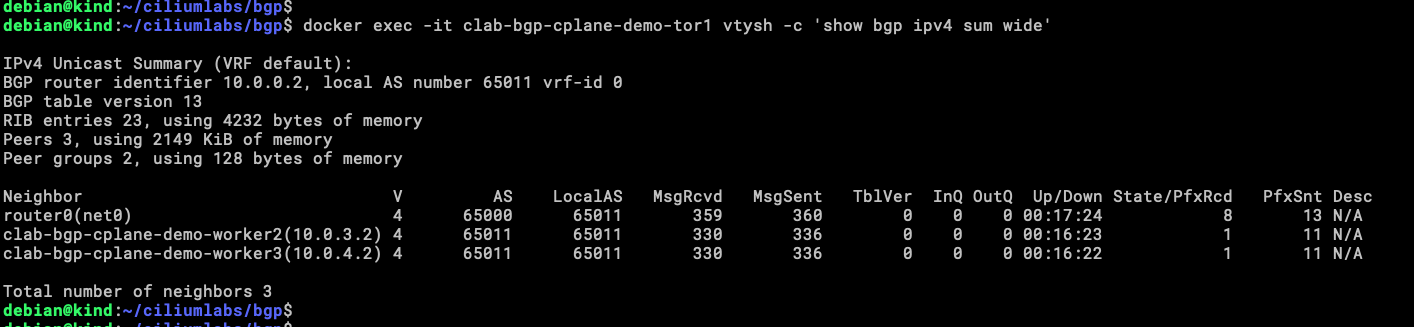
Same for tor1, here the segmentation is called Rack1, and worker2 and worker3 are establishing BGP session!!
Now what?
From here you can go to the official Cilium Labs and earn a badge for Cilium with BGP!
https://isovalent.com/labs/cilium-bgp/
Deja una respuesta